Bad Behaviour for WackoWiki
| implemented as extension Compatible with: R6.1 Current version: 0.8 Credits: Sergey Martynoff, WikiAdmin, RideSnowNow |
It is not in Bad Behaviour release yet, so you can download it here:
1. About
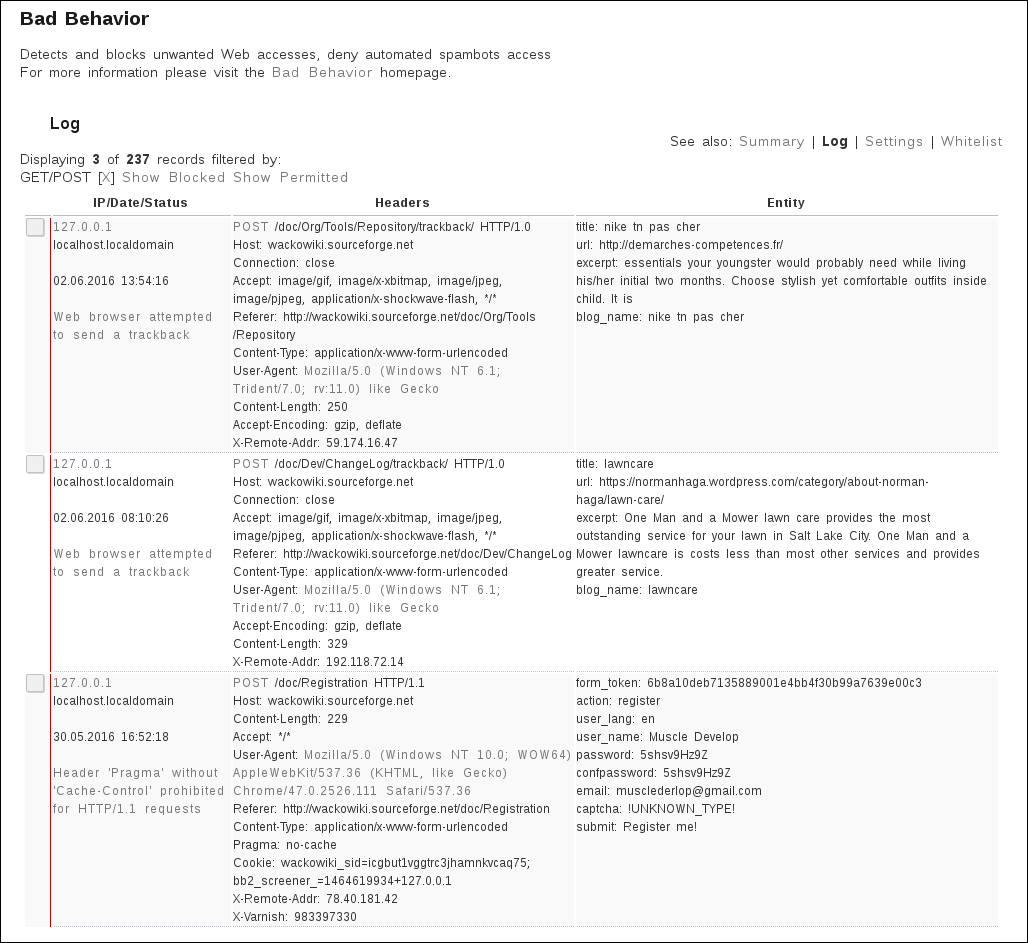
Bad Behaviour is a spam protection system that detects and blocks unwanted Web accesses.
- https://github.com/Bad-Behaviour/badbehaviour
- http://web.archive.org/web/*/h[...]or.ioerror.us/about/
- http://web.archive.org/web/*/h[...]pport/configuration/
- http://web.archive.org/web/*/h[...]rror.us/support/faq/
2. Download
1. Bad Behavior:
2. Bad-Behaviour plugin for WackoWiki:
Put the files in the following folders:
| file | folder | notes |
|---|---|---|
| 1. Bad-Behaviour | ||
| bad-behaviour/ | lib/bad_behaviour/ | move the entire bad-behaviour/ folder here |
| bb_whitelist.conf | config/ | you must create this file, see bb_whitelist-sample.conf |
| 2. Bad-Behaviour plugin for WackoWiki | ||
| tool_badbehaviour.php | admin/module/ | optional, allows you to check the logs, access via admin panel |
| bad-behaviour-wackowiki.php | lib/bad_behaviour/ | plugin for WackoWiki |
| bb_settings.conf | config/ | see Configuration |
3. Installation
To activate the extension you have to set ext_bad_behaviour to 1 in the the Secondary Config, you can do this via the Admin panel.
Admin panel: Extensions -> Bad Behaviour -> Settings
That's all - now go to your site and check if it is still working.
3.1. Configuration
still uses the bb_settings.conf
config/bb_settings.conf
; settings.ini [settings] display_stats = true strict = false verbose = false logging = true httpbl_key = "" httpbl_threat = 25 httpbl_maxage = 30 offsite_forms = false reverse_proxy = false reverse_proxy_header = "X-Forwarded-For" ;reverse_proxy_addresses[] = ;reverse_proxy_addresses[] =
Just as a reminder, if you use CloudFlare, Incapsula, Amazon Elastic Load Balancer, Azure Load Balancer, Google Cloud Load Balancing, or similar services on your site, you may need to enable the Reverse Proxy option in Bad Behavior’s settings, or many of your visitors and search engines will be blocked.
3.2. Whitelist
still uses the bb_whitelist.conf
config/bb_whitelist.conf
; whitelist.conf ; ; Inappropriate whitelisting WILL expose you to spam, or cause Bad Behavior ; to stop functioning entirely! DO NOT WHITELIST unless you are 100% CERTAIN ; that you should. ; IP address ranges use the CIDR format. [ip] ; Digg whitelisted as of 2.0.12 ip[] = "64.191.203.0/24" ip[] = "208.67.217.130" ; RFC 1918 addresses ip[] = "10.0.0.0/8" ip[] = "172.16.0.0/12" ip[] = "192.168.0.0/16" ; User agents are matched by exact match only. [useragent] useragent[] = "Mozilla/4.0 (It's me, let me in)" ; URLs are matched from the first / after the server name up to, but not ; including, the ? (if any). The URL to be whitelisted is a URL on YOUR site. ; A partial URL match is permitted, so URL whitelist entries should be as ; specific as possible, but no more specific than necessary. For instance, ; "/example" would match "/example.php" and "/example/address". [url] url[] = "/example.php" url[] = "/openid/server"
4. AdminPanel Module
5. Changelog
0.1 Intitial version
0.2 Ported to WackoWiki 5.1.0
0.3 Added module for Admin panel
0.4 Integrated in distribution as extension
0.5 Adapted for WackoWiki's new init system
0.6 Removed obsolete cookie related code
0.7 Localized all message sets
0.8 restart Bad Behaviour, see repo
6. To Do
- make use of secondary config
- add notes for ideas, improvements